The Ransomware Playbook Mistakes That Can Cost You Millions
If there is one type of cyber-attack that can drain the color from any
security leader’s face, it’s ransomware. A crippling, disruptive, and expensive
attack to recover from, with
final costs rarely being easy to foretell. Already a prevalent threat, the
number of ransomware attacks rose during the pandemic and nearly doubled in the year
between 2020 and 2021, continuing to rise since.
Focusing on the extortion price of these attacks, the cost of a ransomware attack can appear finite at first, but as costs accumulate over time, and include the entire recovery project, they can reach exorbitant amounts of money. In some cases,
But although these attacks raise concerns from the IT security team all
the way to the board of directors, it appears that companies are not investing
enough in being prepared for such a scenario.
According to the 2022
Cost of a Data Breach Report, the average ransomware attack took 237 days to
identify and 89 days to contain, for a total lifecycle of 326 days. This is
well over 10 months, and those are just the initial stages of the response
process. Furthermore, compared to the overall average lifecycle of regular data
breaches (277 days), it took 49 days longer to identify and contain a ransomware
attack, for a difference of 16.3%. The longer the attackers get to dwell, the
more damage they can cause, and leverage they can eventually gain for the
extortion phase.
Building preparedness for a ransomware attack can translate into shorter
timelines, saving a lot of work and money in the process.
The
Untested Plan…
What if your organization is one of those who already thought a plan was
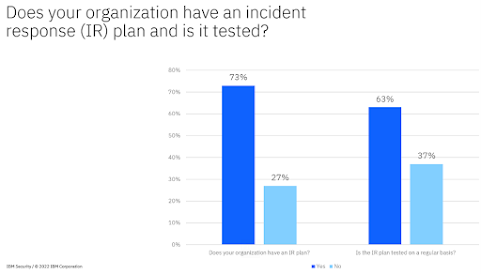
needed, and might have one in place, but this plan was never tested? The 2022 Cost
of a Data Breach report found that of the organizations that had incident
response plans, 37% said they did not regularly test them. Consider the
following question: “How well will you fare if you test that plan for the
first time when you are under an active attack?”
With proper pressure applied, plans can crumble when you most need them.
This is readily easy to infer by looking at the numbers from actual attacks. Organizations
with IR capabilities saw an average cost of $3.26 million per breach in 2022,
compared to $5.92 million for organizations without IR capabilities, a difference
of $2.66 million, or 58.%. A very significant difference.
Moreover, that's an increase in savings over the numbers we saw in 2021,
when the average cost of a breach at organizations with IR capabilities saved
$2.46 million; or in 2020, when the cost difference was $1.77 million, indicating
the growing cost-saving effectiveness of IR capabilities. So have a plan
and test it. You’ll save a lot of time, money, and stress in case of an actual
adverse event, and it sure makes its own business case.
Figure 1: Organizations have plans they do not necessarily test (source: 2022 Cost of a Data Breach report)
More
Organizations Have Plans, But Lack Playbooks
It's not all bad news. Nearly three-quarters of organizations in the 2022
Cost of a Data Breach study said they have an incident response (IR) plan, and
63% said they do regularly test the plan.
But while this is a good start, general technical response plans are
incomplete without scenario-specific plans for major impact, like ransomware. A
Ponemon survey, sponsored by IBM Security, found that security response efforts
were hindered by a lack of specific playbooks for common attack types—and
ransomware has become rather common.
With double or even triple extortion schemes
rampant nowadays, a ransomware attack can have your team facing a number of aspects
simultaneously:
- -
Data breach with privacy and regulatory implications
- -
System disruption without immediately known recovery times
- -
Disaster recovery in case of a destructive attack
- -
Dealing with extortive DDoS
- -
Negotiating with criminals
This sort of complex response requires orchestration of your technical
and executive teams simultaneously. It all needs its own playbook as an
extension of the Cyber Security Incident Response Plan (CSIRP) you might have
in place. That’s assuming that your CSIRP has the adequate maturity level to
pull the organization through a ransomware crisis.
Catch
Up with Playbooks
While security response planning is slowly improving, most organizations
surveyed by Ponemon (74 per cent) are still
reporting that even their technical response plans are either ad-hoc, applied
inconsistently, or that they have no plans at all. Amongst those with a formal CSIRP,
only 17% of respondents had also developed specific playbooks for common attack
types. Playbooks for ransomware and emerging attacks lagged even farther
behind.
These statistics could be driving higher stress and costs on
organizations in an already stormy situation. Having scenario-specific playbooks
in place allows organizations to prepare for emerging attacks that may be
nuanced in the need for decision-making authority and cross-organizational implications.
It also means being able to fall back on an agreed-upon process that distills
the knowledge and experience of your most experienced leaders into a solid,
repeatable process that can be followed to the letter by even the greenest of
new recruits.
Crisis
Management: A Dangerous Gap
Beyond the need for a technical ransomware playbook, there is dangerous
gap to mind that is often ignored when it comes to ransomware attacks. That gap
is the executive response to a crisis that impacts the entire
organization.
A disruptive extortion case will very quickly require escalation to
executive teams, the CEO, and even the board, in ways that other attacks rarely
do. These leaders will have to face the media and impacted parties in short
order, and they will have to be prepared to make decisions using time they do
not have. The results are often more catastrophic than the breach
itself, as leaders can fumble in front of TV cameras and are
may not clearly drive the messages that can best protect the company’s
hard-earned reputation. These situations can go to the extreme with rash decisions that end up
costing the company and its leadership dearly years after the event.
Seeing these cases unfold in the media, executives and boards are taking
a more active approach and seeking to understand their role in a potential
cyber-attack or a cyber crisis. They do that to prepare themselves for the risk
of major monetary loss, potential insurance pushbacks, and even personal
liability. As a result, security leaders are being asked to show and prove
preparedness and demonstrate how the entire company will orchestrate an
adequate response. One way to show this preparedness is a playbook that can
engage these executives early on. Equipping executives with plans, process,
templates for communications, and clear lists with contact information can save
them the stress and time they need to make swift decisions and drive the
company through and out of the crisis successfully.
These plans can also help make and document decisions in advance with a
cool head, extending the ‘commander’s intent’ through to other team members that
will use the plan under fire, even as they pivot through the event’s turns. Build
a plan, drill the plan, and have metrics and KPIs to show your organization is
prepared and keeps improving.
Ransomware
Playbooks – the Essentials
Having a plan for responding to a ransomware attack begins with the
basics of incident response. Let’s take the NIST framework as a standard
for this purpose.
Figure 2: NIST IR Framework: Identifyà Protectà Detectà
Respondà Recover (source: NIST)
Within the framework, zooming in on the “Response” section, we
have:
- -
Preparation
- -
Detection and Analysis
- -
Containment, Eradication, Recovery
- -
Post Incident Activity
Preparing to handle incidents is the phase where plans are
drafted and tested, then drilled and updated over time. It’s an essential part
because it impacts the quality of response that will eventually take place.
Detection and Analysis are the port through which your organization realizes
there is an incident to handle. This is where Triage takes place to assess
severity and have an initial idea of impact and root cause. It’s also the
process starts to escalate to the parties who will carry out the technical
response in the next stage. In the case of ransomware, this is where your
technical management will also inform relevant executives.
Containment,
Eradication, and Recovery activate
your incident management teams and guides them through escalating to staff members
that manage
platforms, infrastructure and applications that may be impacted. It could be
that this plan also covers data loss cases, and it may or may not account for
both IT and security, but all these aspects will go into the effort to
minimize damage and restore access and services as quickly as possible.
Before moving to any post-event activity, where do ransomware playbooks
come into the picture? They have to be worked with in parallel:
-
They should be part of the preparation, providing plans
that can guide teams through response that’s specific to ransomware attacks and
their nuanced nature. This preparation should aim to prevent incidents and it
should outline when and how the organization may use backups in a recovery
process. Your executives must be consulted here if service impact is going to
affect the organization’s reputation, employees, customers, revenues, etc.
Hence, again, the preparation of playbooks is essential.
-
A ransomware playbook should contain qualification criteria
and thresholds that would allow ransomware to be called out immediately upon detection
and analysis, and thus escalated accordingly to technical management but
also to the CISO, CIO, Chief Legal and other executives.
-
The ransomware playbook should be used in the containment,
eradication, and recovery stages. Unlike incidents that urge availability
above other considerations, a ransomware case prioritizes ensuring that endpoints,
servers, databases, cloud, and other assets, are recovered safely and after
they have been cleared (and cleaned) for going back online.
Evidence
preservation for a ransomware case should also be specific and carried out
appropriately. This will allow the organization to later work through potential
legal and forensic investigations.
And this is not all.
A
View from the C-Suite
Ransomware is a ticking time bomb that requires a lot of involvement
from the executive team. There are whole-of-business considerations, decisions,
negotiations, budgeting, regulatory, HR, finance, legal implications, and strategic
approvals that go into the overall attack lifecycle, to name a few. None of
these are accounted for inside a classic, technical CSIRP.
A separate playbook, drafted from a strategic viewpoint, has to be
crafted with participation of your C-suite executive team, to ensure that they
come together and understand what’s needed of them quickly when an attack
advances rapidly.
They will need to see how a pre-approved qualification criteria
triggered a crisis level alert. They will ask to see a business impact analysis
from the technical team. The Business Continuity team will have to present
information from their end, as will the Disaster Recovery team. Looking at a threat
intelligence brief on the suspected group that attacked the organization will
enable executives to understand the motives and modus operandi and further help
them make the right decisions with the data they have.
At this time, where time is the last thing they have, your organization would
want to rely on pre-made decisions and intent established ahead of an actual
attack – when you had the chance to plan and think through the burning
questions. Will you consider paying a ransom? What are the conditions you would
pay under? What if paying is a federal offense in this case? Will you call a
negotiator? What is the holding statement your CEO plans to give the media when
that first call comes in? Was it approved by Comms and Legal?
All these questions can, and should be, answered in advance, in a
designated executive ransomware playbook.
Back to the NIST framework, we are at the Post Incident Activity
stage. This is where company-wide coordination should gather the event logs and
lessons learned from all those who were actively involved in the incident, and
those who experienced it from the sidelines.
Feedback sessions should allow both technical and executive management
to be open and candid in their viewpoint, without blaming anyone, working to improve
the plans and their execution to prevent breakdowns in potential future events.
In the 2022
Cost of a Data Breach report, 83% of respondents indicated that their organization
has already gone through more than one data breach. With attack numbers only
growing year over year, getting better at handling them must be part of how
businesses are run.
Figure 3: Most organizations have already suffered more than one breach (source: 2022 Cost of a Data Breach report)
For the complete 2022 Cost of a Data Breach report, please click: ibm.biz/breach-report
Six steps for building a robust incident response strategy: https://www.ibm.com/security/digital-assets/soar/six-steps-for-incident-response
Planning for Cyber Crisis Management: https://www.ibm.com/downloads/cas/KMBQMBMW
Want to learn more about how an incident response retainer can help your
organization? Check out https://www.ibm.com/security/incident-response
This post was originally published by IBM Security: https://securityintelligence.com/posts/ransomware-playbook-mistakes-cost-you-millions/




Comments
Post a Comment