Shedding Light on the DarkSide Ransomware Attack
It has been well over a decade since cybersecurity
professionals began warning about both nation-state and financially motivated
cyber-kinetic attacks. Concerned about a cybersecurity threat that would have
the potential to destroy physical assets and human lives, many looked to sound
the alarm in industrial organizations, tracking the vulnerabilities that could
lead to a compromise in operational technology networks.
A variety of attacks in that realm took place over the
years, whether launched in nation-state conflicts across the globe or as an
apparent amateur challenge. Most recently, cybercriminals who deploy ransomware
targeted a large U.S. refined products pipeline system, causing disruption to
its operations and making headlines across the world. The attack reportedly
only affected IT networks but had the potential to spread to operational zones
and upstream to the overall supply chain — an attack scenario that could be
much more damaging.
Unlike many attacks on industrial organizations that
have been connected to adversarial nation-states, it seems that the pipeline
attack might be a cybercrime case motivated by a large bounty. The group
suspected in this hit goes by the name “DarkSide.”
IBM Security X-Force data shows that ransomware has
become the number one threat type X-Force responded to in 2020 accounting for
23% of actual attacks that impacted organizations. Of those, our incident
response data shows 59% of attacks were double-extortion cases, where in
addition to having their data encrypted, victims were also threatened with data
being leaked unless they paid for a decryption key by a specified deadline.
X-Force incident response data further shows that
ransomware attacks were the most common threat to organizations that use
operational technology (OT) in 2020. Sectors we examined in our data include
manufacturing, oil and gas, transportation, utilities, construction, and
mining, where ransomware attacks accounted for 33% of all attacks we responded
to. This trend suggests that threat actors may be finding organizations with OT
networks to be particularly attractive for ransomware attacks precisely because
of the costly downtime and impact on a wider ecosystem and on individual
consumers.
Who is on the DarkSide?
In August 2020, a new ransomware gang announced its
entry into the cybercrime arena. In no less than a “press release” of sorts,
its operators declared they had developed the perfect ransomware tool because
other codes they used in the past were not up to the task. The post appeared on
the group’s TOR domain where the newcomers also advised they were not
inexperienced cybercriminals and acted as former affiliates to other successful
gangs, making millions of dollars in the process. The malware itself has small
similarities to the GandCrab and Sodinokibi ransomware, as does the ransom
note’s template. Another similarity is that DarkSide is designed to avoid
computers where a language layout corresponds with one of 17 countries from the
former Soviet Union, adding Syrian Arabic — another similarity to Sodinokibi.
When looking for affiliates to join their ranks, tech-savvy Russian speakers
need apply. They further stress that they are not interested in “English
speaking personalities.” DarkSide has
also noted that while they plan to target organizations, they would aim for
those who ‘can pay’ and spare healthcare, schools, non-profits, and government.
New Group, Old TTPs
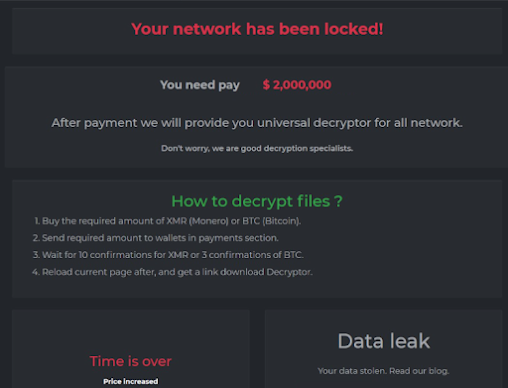
Like other gangs that operate modern ransomware codes,
such as Sodinokibi and Maze, DarkSide blends crypto-locking data with data
exfiltration and extortion. If they are not initially paid for a decryption
key, the attackers threaten to publish confidential data they stole from the
victim and post it on their dedicated website, DarkSide Leaks, for at least 6
months. When a ransom note appears on an encrypted networked device, the note
also communicates a TOR URL to a page called “Your personal leak page” as part
of the threat that if the ransom is not paid, data will be uploaded to that
URL. Ransom is demanded in Bitcoin or Monero. If it is not paid by a specific
initial deadline, the amount doubles.
Read on here.

Comments
Post a Comment